Blogs
Microsoft Ignite 2025: the ‘need-to-know’ highlights
Catch our comprehensive summary of the highlights from Microsoft Ignite 2025, combined with the resources and links you need to dig into the detail!

Ransomware attacks can destroy small and medium businesses (SMBs). So real is the threat, new legislation under consideration by the Australian federal government presents possible penalties for making payments.
There is increasing concern amongst policymakers that paying off ransomware attackers encourages ever bolder and more daring criminal behaviour. Recent media reports outline the Australian federal government is reviewing existing regulations as part of its “Ransomware Action Plan’.
New rules would introduce a ‘zero tolerance’ position on ransomware, making it mandatory for all companies with turnover of more than $10 million per annum to report ransomware attacks and disclose any associated payments made.
There is continued debate about the impact and efficacy of the proposed changes, but it is a clear signal the government intends to act. We encourage our partners to keep a close eye on this issue and raise awareness with their customers that ransomware attacks on small businesses are on the rise.
Let’s be honest, many SMB owners wrestle with prioritising cyber security. They’re focused on building their business, adding new clients, managing cash flow and keeping the lights on in their operation.
Time and resource are scarce and stretched across a myriad equal and competing business needs, such as customer service, sales, products, marketing. The focus is on activities and investments that grow the business, not so much the stuff that could derail it, like ransomware attacks.
One of the challenges for SMBs in accepting ransomware as a risk is the terminology sounds like something out of a spy movie – more like fiction than fact. There is also a common misconception that cybercriminals only target big business, as these stories are the ones that tend to make headlines.
In reality ransomware is a direct threat to SMBs in Australia and New Zealand, which are both in the top ten of nations targeted by this type of attack. Corewave also reports the average downtime caused by ransomware attacks due to recovery of data and restoring networks is 16.2 days – which would be devastating for most small businesses.
Ransomware statistics can be scary, but they don’t reveal the horror nor human suffering behind the numbers. The harsh reality is ransomware can send businesses to the wall, and more businesses are at an increased risk of this kind of attack than ever.
The good news is SMBs can minimise risk by adopting the Essential Eight cybersecurity framework. Devised by the Australian Cyber Security Centre (ACSC), adherence to the recommended controls in the framework massively reduces SMB exposure to ransomware attacks as well as other cybersecurity threats.
For SMBs at the start of their cyber security journey, the Essential Eight removes a lot of concern and complexity because ACSC cyber security experts have done most of the thinking and planning required to get cybersecurity measures right. They’ve identified the major threats and listed actions to mitigate them. It’s a joined-up cyber security action plan. For cost-conscious SMBs, the good news is the Essential Eight is free expert consultancy.
The following two mitigations from the Essential Eight provide an example of effective risk management that will give all SMBs a better chance of combating cybercriminals.
This mitigation action calls for regular data and systems backups (at least daily). Many online businesses need more frequent backups so they can restore systems and data to a very recent position. SMBs should implement a backup frequency that suits their specific conditions.
This mitigation also recommends regular testing of the recovery process. Testing proves that the backup solution works, and that data can be restored in the event of a ransomware or other attack.
The ACSC says: “Multi-factor authentication is one of the most effective controls an organisation can implement to prevent an adversary from gaining access to a device or network and accessing sensitive information.”
MFA requires users (whether inside or outside the organisation) to provide two or more types of authentication (e.g. username and password, plus a finger or eye scan, or a PIN texted to their phone). MFA makes it much harder for hackers to get access to a system through stolen login credentials.
The Essential Eight is the outcome of some serious thinking by highly talented ACSC cyber security experts and provides a practical and realistic starting point for many SMBs to prevent ransomware and other attacks. The fact that it’s also free just makes it even more compelling.
For our partners, Crayon offers a service that can help you to assess the state of your customers Essential Eight maturity levels. It is a practical and effective way to identify where they have existing risk and get an actionable roadmap in place that will improve their cybersecurity posture.
Whether you have an existing security practice or need new ways to respond to your customers increased security needs, our Security Assessment services have you covered.
Learn More about how we can help.
Blogs
Catch our comprehensive summary of the highlights from Microsoft Ignite 2025, combined with the resources and links you need to dig into the detail!

Training
In our latest webinar, our in-house Modern Work experts Jye Wong and Ksenia Turner will run you through a practical refresher on Solution Partner Designations; what they are, why they matter and how to get started.

Sales and Marketing
Business leaders don't live in the tools. They live in the outcomes. The metrics they care about most are not always limited to compliance and risk. So how do you connect data protection to the big-ticket objectives, when they're less obvious? Our in-house pre-sales expert, Michael Brooke explains.
Guides and eBooks
As SMBs mature in the Data Protection lifecycle, they need help to optimise spend, reduce the compliance burden and ensure results align to business objectives. The third installment of our Data Protection Playbook series provides practical guidance for partners on how to address emerging pressure and connect ongoing investment to measurable business value.
Training
Copilot Agents: what are they and how do they differ from AI assistants and chatbots? Our in-house Copilot expert Ksenia Turner explains the use cases and service opportunities for partners.

Blogs
Fragmented data protection systems and processes create compliance proof-gaps for SMB customers. Scott Hagenus, Director, Cybersecurity here at Crayon explains.

Guides and eBooks
How can partners help their SMB customers to move from silos of security and continuity to a more cohesive, measurable and insurable data protection framework? The second edition in our Data Protection Playbook series maps out their journey, and yours.

Sales and Marketing
Ever wonder why a pitch has some IT Managers leaning forward, while others glaze over? Michael Brooke, Cybersecurity Pre-Sales Lead offers some insight on how to tune your approach to chime with different technical mindsets.

Vendor Announcements
Copilot for Business has landed at Microsoft Ignite 2025, levelling the GenAI playing field for SMB customers. Learn all about it from our man on the ground, Andreas Bergman.

Press Release

Press Release

Blogs
As cybersecurity and continuity converge in platforms and in practice, partners need new playbooks to address modern Data Protection standards. Our in-house cybersecurity pre-sales lead, Michael Brooke explains why.

Guides and eBooks
What triggers an SMB customer to begin exploring their need for better Data Protection? The first of our four Data Protection Playbooks for partners breaks down how to position and win in the Pre-Adoption and Exploration stage.

Insights
Data Protection priorities are shifting for SMBs. Ramp up your ability to respond with curated insights, articles and resources to help you guide every customer conversation with confidence.

Partner Spotlight
In this Partner Spotlight, Acceltech Managing Director Ivy Tarrobago shares how Crayon’s responsive support enhances client outcomes and business growth.

Whitepapers
Data Protection is a must for all SMBs but how can partners align solution investment with critical business objectives? Our latest paper shows you how.

Press Release
Crayon has been recognised with a huge double win at the CRN Channel Asia awards ceremony.

Insights
All the latest insights, articles and resources on M365 Copilot, curated into one place.

Insights
SMB customers are storing greater volumes of sensitive data in more places than ever. Secure backup and recovery practices are essential to how they protect it.

Partner Spotlight
Bigfish Technology saved AU$20,000 on its annual Microsoft licensing after one call with Crayon and has since built a strong partnership that enabled Bigfish to get access to Crayon’s expertise and vendor ecosystem.

Insights
Insider risk is a subtle and continuous challenge for SMB customers. Turn it into a manageable and quantifiable aspect of their Data Protection strategy.

Blogs
From rethinking backup to governance frameworks and behavioural analytics, what's involved in building a complete Data Protection strategy for SMB customers?
Insights
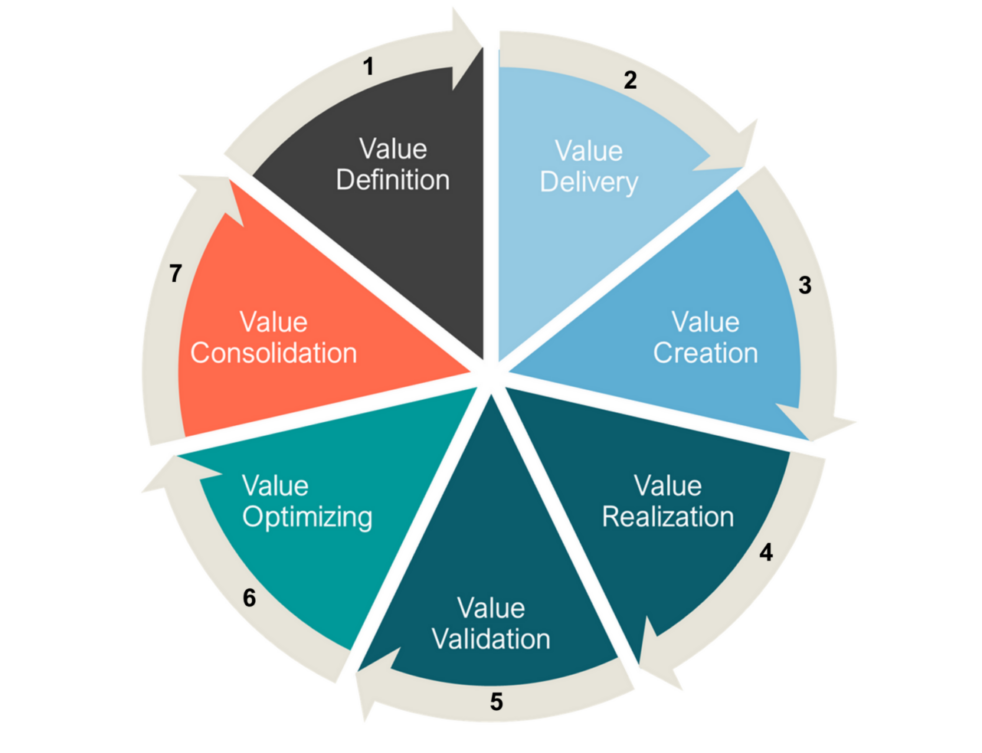
We explore the evolution of Microsoft's channel strategy over the past ten years, and what can be learned by viewing it through a Value Cycle lens.

Guides and eBooks
The Microsoft Fabric Partner Guide curates our recent articles, videos and resources to accelerate Crayon partner learning.

Insights
Support your cybersecurity game plans with our top picks of new and updated risk and resilience resources.

Webinars Series
How do security assessments empower your cybersecurity practice to respond to the rise of AI? Find out!

Webinars Series

Case Studies
Essential Eight Compliance can be tough to maintain for partners and customers. Learn how Airlock simplified the challenge for one MSP, and delivered faster time to value.
Press Release

Podcast
Cybersecurity experts from Crayon, SMX and Red Sift cover the realities of the complex threat landscape and how partners can respond.

Company Announcements

Press Release
Empowering Partners, MSPs and ISVs with best-in-class protective DNS security solutions
Blogs
Crayon cloud security assessments help partners lock down M365 and Azure environments and build profitable cybersecurity practices. Learn how.

Blogs

Connect Data Protection to strategic objectives via this Whitepaper

What are the most critical business objectives and solution adoption priorities for SMBs in our region? Download the latest Forrester study to find out!

Our APAC channel business is now part of a global organisation. That means there is a whole new world of value on offer for our partners. We can help you to tap into all of it.